¶ Overview
The Defend-O-Tron is a transparent inline security appliance for small and medium businesses — the segment that needs serious protection but typically can't justify the budget, staff, or multi-year subscription contracts of enterprise vendors like Cisco, Fortinet, Sophos, or Palo Alto.
It sits between your ISP modem and your firewall, inspects every inbound and outbound packet in real time, and silently blocks malicious traffic before it reaches your network. To an attacker probing your public IP, everything behind the appliance looks like closed stealth ports — not a target worth pursuing.
The Defend-O-Tron's defense engine is powered by CrowdSec and its firewall bouncers, augmented with Suricata for deep packet inspection on both ingress (ISP → you) and egress (you → internet) traffic.
When the appliance catches a malicious IP, the block applies locally and the address is shared with the CrowdSec community. Every other Defend-O-Tron — plus every other CrowdSec-equipped system worldwide — picks up the block within minutes. Your protection improves as the community grows; an attack caught somewhere else lands as a pre-emptive block on your device.
Read more about our open source commitment here Opensource Matters
¶ What's Actually Happening Out There
The numbers below are from major security vendors' most recent annual reports — they sketch the texture of what's hitting your network, not a hypothetical worst case. Most SMB owners we've spoken to recognize at least one or two of these from their own experience.
- Ransomware victim counts climbed sharply in 2025. Fortinet's 2026 Global Threat Landscape Report tracked 7,831 confirmed ransomware victims in 2025 across manufacturing, business services, and retail — the sectors most SMBs operate in or supply (FortiGuard Labs Global Threat Landscape Report). If you've read a local news story about a supplier or peer business being hit, this is the data behind it.
- Internet-wide reconnaissance is industrial-scale. FortiGuard observed over 36,000 port-scans per second globally in 2024. If you've noticed your router logs filling with blocked connection attempts from random IPs around the world, that's why.
- The patch window has collapsed. Critical vulnerabilities are now being exploited within 24-48 hours of disclosure (Fortinet) — down from roughly five days a few years ago. Patching on a Friday is no longer fast enough; perimeter blocking matters more than ever.
- Stolen credentials are everywhere. Fortinet tracked a 42% jump in stolen credentials traded on darknet forums in 2024 — more than 100 billion unique records of emails, passwords, session tokens, and MFA-bypass data. If you've received a "your email was in a breach" notification, you've already met the supply side of this market.
- Community defense actually multiplies. The CrowdSec community blocklist aggregates attack data from tens of thousands of participating devices and rotates roughly 5% daily for fresh threat intel. For every attack a single device's security engine catches, the community blocklist has typically pre-blocked 25 to 40 other attempts before they reached the engine. The Defend-O-Tron taps that multiplier automatically.
If two or three of these read as "yeah, I've heard of that" — or, more likely, "I know someone who was hit" — you're the audience this device was built for.
¶ Why Defend-O-Tron Fits SMBs
The biggest gap in most SMB security postures isn't the absence of expensive products — it's the absence of someone to run them. ISC2's Cybersecurity Workforce Study reports roughly 4 million unfilled cybersecurity positions globally, and almost none of those candidates work for businesses with under 500 employees. SMBs that do have IT staff rarely have dedicated security staff.
The Defend-O-Tron is built for this reality:
Drop-in and walk away. Cable it in between your ISP and your router. No client software on any device. No agents. No per-device configuration. The whole public network side of your router is protected.
Self-updating. Firmware, threat intelligence, IDS rules, and the underlying OS all update automatically. The day-to-day operational burden is approximately zero.
Self-defending. The CrowdSec community contributes attack data from tens of thousands of devices; your appliance benefits from every one of them.
Audit-ready from day one. When your insurance broker, an auditor, or a customer asks for evidence that you're protecting their data, one terminal command produces a signed evidence ZIP covering whatever period they need.
Removable in seconds. If anything ever feels off, unplug the device and you're back to your original network in less time than it takes to reach support. No "rip out the security stack and find another vendor" recovery scenario.
One device, one set of credentials. The whole network shares one admin login, one Root CA to install on your workstation, one configuration to back up.
The result: protection that doesn't require building (or renting) a security team — but that holds up when an auditor, an insurer, or a customer asks the hard questions.
¶ What You Don't Have to Pay Extra For
If you've shopped SMB security appliances from the major vendors, the pattern is familiar: the hardware is one line item, then layered "security service" subscriptions stack on top — IDS/IPS, threat intelligence, DNS filtering, application control, sandboxing — each commonly sold as part of an annual or multi-year subscription bundle.
This is the long-established UTM market pattern. As TechTarget's UTM market analysis documents, "UTM appliances share a set of basic features … and the vendors require the purchase of a license or subscription for those modules." Concretely: Fortinet bundles services under FortiGuard, Sophos under FullGuard, WatchGuard under Total Security Suite, and SonicWall under Comprehensive Gateway Security Suite. Cisco Meraki goes further — every Meraki hardware component "requires a cloud license or it will not function properly" (the appliance literally stops working when the license lapses). The recurring spend, over the life of a typical 3–5 year deployment, often rivals or exceeds the cost of the hardware.
The Defend-O-Tron includes the equivalents of those subscription line-items in the price of the device:
| Capability | Defend-O-Tron | Common industry pattern |
|---|---|---|
| Threat-intelligence feed | Included (CrowdSec community blocklist + Suricata rules) | Annual security-services subscription (FortiGuard, Sophos FullGuard, WatchGuard Total Security Suite, SonicWall CGSS) |
| IDS/IPS signature updates | Included, daily refresh | Module within the UTM subscription bundle |
| DNS filtering & ad blocking | Included (AdGuard Home) | Module within the UTM bundle, or a standalone DNS-filter SaaS |
| Compliance audit evidence | Included (Ed25519-signed daily manifests, on-demand evidence ZIPs) | Standalone compliance-automation SaaS (Vanta, Drata, Tugboat Logic) |
| Centralized dashboards | Included (pre-built Grafana panels: cyber-threats, CrowdSec metrics, NIS2 evidence, Traefik, system status) | Separate SIEM product or per-device cloud-dashboard licence |
| Cloud licence to keep hardware running | Not required | Required on some platforms (e.g. Cisco Meraki) |
| Firmware & security updates | Included for the life of the device | Often gated behind an active support contract or maintenance subscription |
| Sharing decisions with external bouncers | Included (LAPI for nftables, NGINX, Traefik, MikroTik, pfSense) | Generally not packaged as a separate-vendor offering |
For IT consultants and MSPs: the Defend-O-Tron's no-subscription posture changes the conversation. Instead of building your service offering around someone else's renewal calendar, you decide what to charge for — monthly audit-evidence handover, threat-intel triage, SIEM integration on your side, or just hands-off perimeter protection. Recurring revenue lives in your service tier, not in a device-vendor price list you don't control.
¶ Why Defend-O-Tron
Defense and audit evidence, in one box. Most security appliances detect attacks. The Defend-O-Tron also proves it did — every event signed, every day, ready to hand to your NIS2 / SOC 2 / ISO 27001 auditor as a single signed ZIP. The kind of capability that's normally a paid SIEM add-on on Cisco / Fortinet / Sophos.
Transparent inline protection. Drops in between your ISP and your router. No agents, no client software, no per-device configuration. If anything ever feels off, unplug and you're back to your original setup in seconds.
Crowd-sourced threat intelligence. Each Defend-O-Tron contributes to — and consumes from — the CrowdSec community blocklist. When the attacker who probed someone else last hour shows up at your door, you already know about them.
Tamper-evident audit evidence. Ed25519-signed daily manifests anchored to NTP-attested time. One command produces a complete evidence ZIP for any past period. Built in, runs automatically. Read more →
In-place firmware updates with rollback. Browser-button updates. The previous firmware stays on the device — switch back in seconds if anything's off. The original factory image is preserved as a last-resort recovery point. Read more →
Share decisions across your fleet. Attach external firewalls, web servers, and reverse proxies to consume the same threat decisions the appliance is enforcing. Read more →
Made in Canada. Designed, assembled, and supported here.
Open hardware. Schematics published. NVMe storage replaceable. Right-to-repair as a feature, not as an afterthought.
¶ Protection Flow
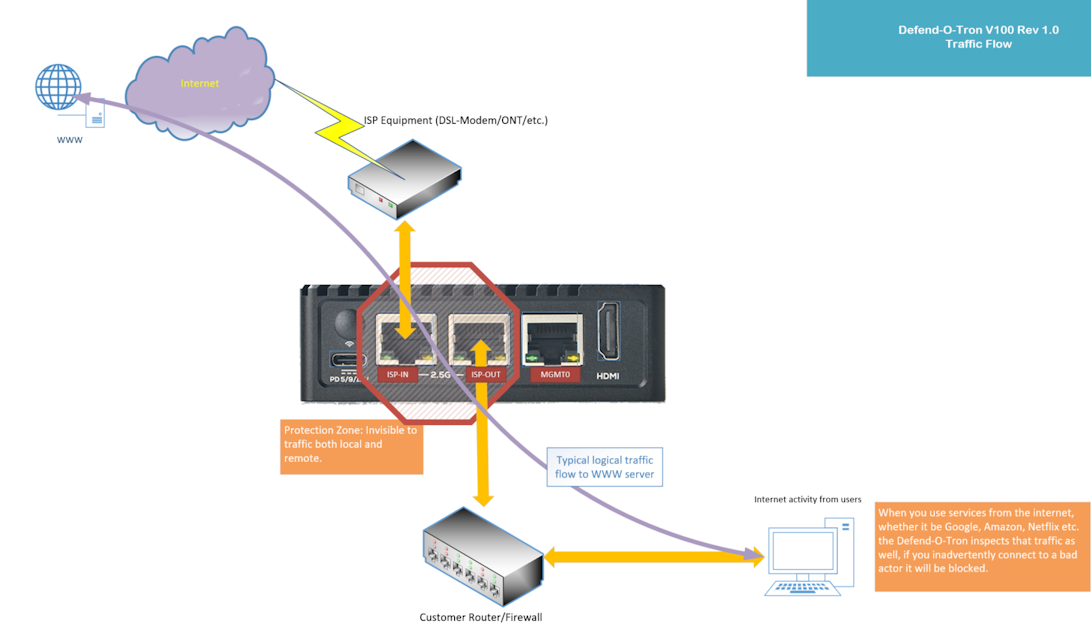
The Defend-O-Tron is transparent to traffic from the ISP to your router/firewall, making any bad actor unaware of it’s presence.
No extra software to install and no special configurations make this a simple design. This allows the Defend-O-Tron to be removed quickly in the event that it could be interfering with data flow to or from the internet, while still being accessable via the management interface. Simply plug your firewall/router back into the ISP equipment as before.
Want the architecture diagram, defense-component inventory, and a live GRC Shields Up protection test? They live on the Under the Hood page.
¶ Getting Started
Your Defend-O-Tron security device is quick and easy to install. You should be up and running in no time.
- Features Worry free defense.
- Requirements Networking and connections.
- Installation Guide Detailed installation instructions.
- Use Cases Typical Networking use cases
¶ Administration
Admin Interface Navigate the Cockpit-based management interface.
Dashboards Cyber-Threat, CrowdSec, NIS2 Evidence, Traefik, and System dashboards.
Compliance Reporting Generate tamper-evident NIS2 Article 21 audit evidence.
Firmware Updates In-place firmware updates with rollback to previous or factory.
Certificates Install the Defend-O-Tron Root CA on your workstation.
CrowdSec API Attach external bouncers to share live threat decisions.
Honeypot Bruteforce-scan trap rules.
DNS Filter Manage the built-in AdGuard DNS filter.
Remote Support Open a temporary, operator-initiated support tunnel.
Telemetry Help developers understand emerging threats with anonymous telemetry.
¶ Feeding Logs
Feed your Defend-O-Tron logs from other devices to enhance the threat detection.
¶ Under the Hood
For the technically curious: how the Defend-O-Tron is built, the components that defend you, and the open-hardware platform underneath.
Architecture Defense components and the protected-zone packet flow.
Protection Test Real-world GRC Shields Up port-scan result.
Hardware Spec What powers the Defend-O-Tron.
Open Hardware Spec Schematics and more.